On Jan. 29th, a record setting personal data breach being hailed as the Mother of all Breaches (MOAB), exposed 26 billion individual personal records discovered by security research firm SecurityDiscovery.com.
The compromised information is known to contain data from past breaches as well as new data. The breach contains user login credentials and other sensitive information that is valuable to malicious actors.
Link to the news story: https://cybernews.com/security/billions-passwords-credentials-leaked-mother-of-all-breaches/
What does this mean for you?
Malicious actors will likely start using information to attack other accounts from compromised users. Attackers will try to use compromised passwords to see if they were reused for more high value accounts like email or banking. Attackers are also likely to send many more phishing attacks and spam emails targeting compromised people.
How can you protect yourself?
Good password hygiene practices are the best way to mitigate the risk of your compromised user login information being used against you to access your accounts.
Password Hygiene Best Practices:
- Use passphrases. Passphrases are a sentence-like string of words that contains a mixture of uppercase, lowercase, and special characters that is easy to remember but hard to hack.
- Don’t reuse passwords or passphrases. Use a unique login for every online account you own. This prevents an attacker from gaining access to all your accounts with minimal effort.
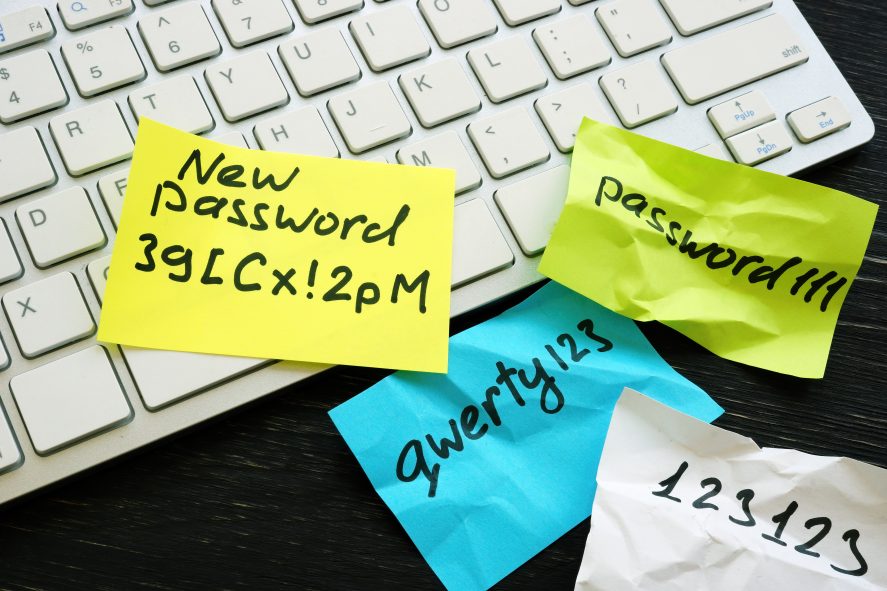
- Use a password manager program. These are applications that store all your passwords in an encrypted database for easy use, can assist in generating new, unique passwords, and sync them across all of your devices. A much better idea than a sticky note.
- Frequently change all your account passwords. Recommendation for password rotation is every 90 days. If that seems too frequent for you, try rotating passwords at least once a year on all your personal accounts.
- Use multi-factor authentication (MFA) whenever possible. Most users are already familiar MFA for their bank or work accounts. This protects accounts from compromise by forcing users to provide their passcode along with a code. Typically, this is provided directly to a user’s cell phone via a one-time passcode or a phone application that pushes a request asking for approval to the device’s screen.
- General cybersecurity awareness training. The state mandates annual cybersecurity training for all employees. This training is designed to help highlight current cybersecurity threats and increase knowledge of how to be cybersecurity aware.